Predefined pipelines reference
AI summary
About AI summaries.
Imply Lumi offers predefined pipelines for the log formats described in this topic. A predefined pipeline extracts fields from the raw event message and creates user attributes you can search. Predefined pipelines are enabled by default.
The following diagram shows a raw log event and how its fields appear in Lumi after processing by the predefined pipeline:
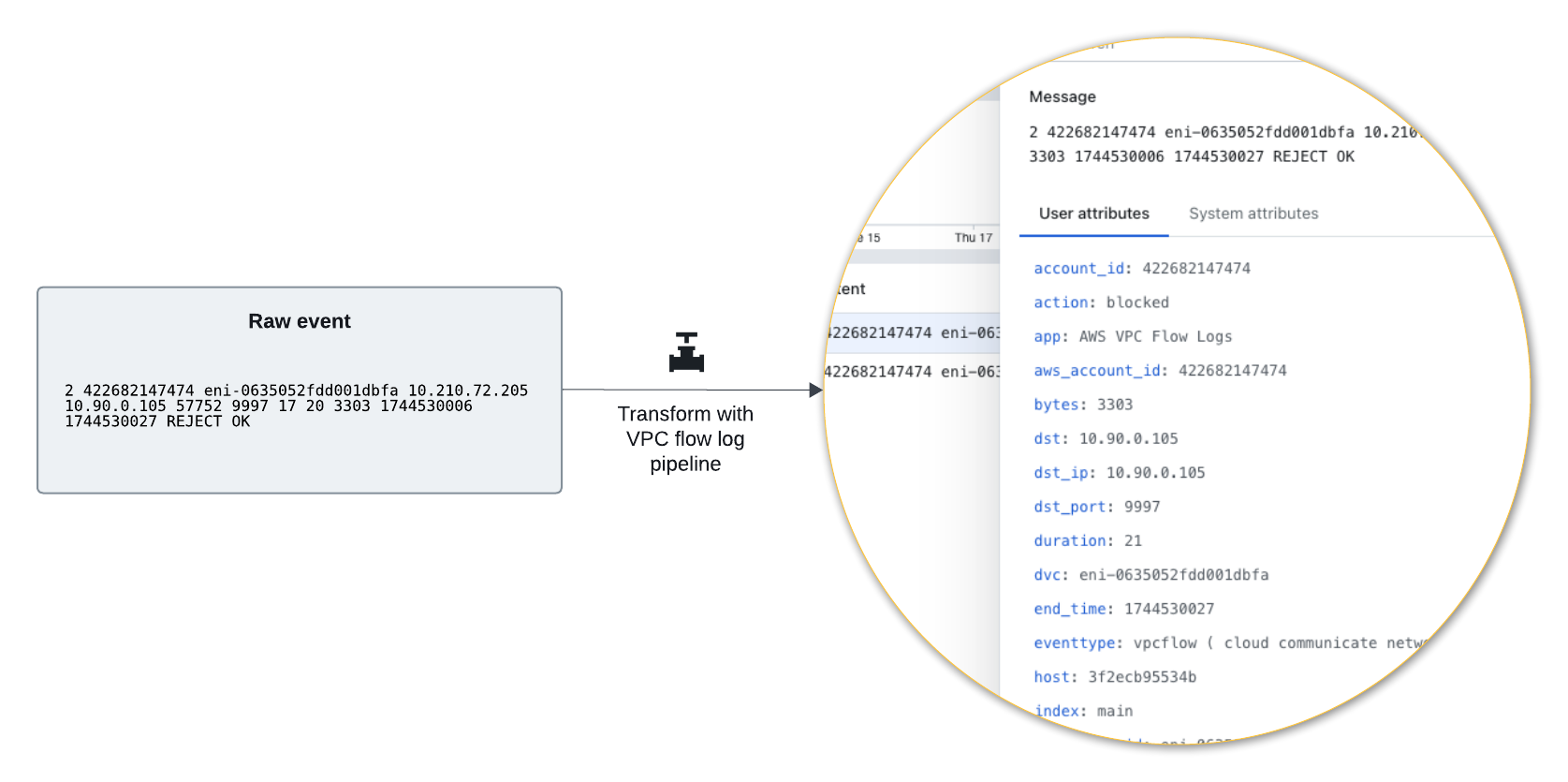
Like other pipelines, the predefined pipeline only operates on incoming events that satisfy the pipeline conditions. If you want to change the conditions or processors, you can use the predefined pipeline as a template for your own custom pipeline.
To learn how to use and manage predefined pipelines, see Work with predefined pipelines.
FortiGate event logs
Pipeline condition: sourcetype="fgt_event"
FortiGate event logs records system and administrative events, including admin logins, reboots, or VPN status. See the FortiGate documentation for example events.
Example of extracted user attributes
{
"action": "success",
"body": "Administrator admin logged in successfully from ssh(172.16.200.254)",
"change_type": "auth",
"date": "2026-02-17",
"dest": "172.16.200.2",
"dest_ip": "172.16.200.2",
"dstip": "172.16.200.2",
"eventtime": "1557771654587081441",
"eventtype": "ftnt_fortigate",
"id": "0100032001",
"index": "docs-fortigate",
"level": "information",
"log_action": "login",
"logdesc": "Admin login successful",
"logid": "0100032001",
"method": "ssh",
"msg": "Administrator admin logged in successfully from ssh(172.16.200.254)",
"product": "Firewall",
"product_version": "50",
"profile": "super_admin",
"reason": "none",
"result": "Admin login successful",
"severity": "informational",
"severity_id": "6",
"sn": "1557771654",
"source": "http:docs-fortigate",
"sourcetype": "fortigate_event",
"src": "172.16.200.254",
"src_ip": "172.16.200.254",
"src_ip_from_ui": "172.16.200.254",
"src_user": "admin",
"src_user_name": "admin",
"src_user_type": "Admin",
"srcip": "172.16.200.254",
"status": "success",
"subtype": "system",
"time": "11:20:54",
"type": "event",
"ui": "ssh(172.16.200.254)",
"user": "admin",
"user_name": "admin",
"user_type": "Admin",
"vd": "vdom1",
"vendor": "Fortinet",
"vendor_action": "login",
"vendor_product": "Fortinet Firewall",
"vendor_status": "success"
}
FortiGate traffic logs
Pipeline condition: sourcetype="fgt_traffic" OR sourcetype="fortigate_traffic"
FortiGate traffic logs records traffic flow information for the traffic that passes through FortiGate to your network. See the FortiGate documentation for example events.
Example of extracted user attributes
{
"action": "allowed",
"app": "HTTP.BROWSER_Firefox",
"appcat": "Web.Client",
"appid": "34050",
"applist": "g-default",
"apprisk": "elevated",
"bytes": "2412",
"bytes_in": "1224",
"bytes_out": "1188",
"countapp": "1",
"date": "2026-02-18",
"dest": "23.59.154.35",
"dest_interface": "port11",
"dest_ip": "23.59.154.35",
"dest_port": "80",
"dest_zone": "undefined",
"dstcountry": "Canada",
"dstintf": "port11",
"dstintfrole": "undefined",
"dstip": "23.59.154.35",
"dstport": "80",
"dstuuid": "ae28f494-5735-51e9-f247-d1d2ce663f4b",
"duration": "116",
"eventtime": "1557513467369913239",
"eventtype": "ftnt_fortigate",
"ftnt_action": "allow",
"index": "docs-fortigate",
"level": "notice",
"logid": "0000000013",
"mastersrcmac": "a2:e9:00:ec:40:01",
"osname": "Ubuntu",
"packets": "33",
"packets_in": "16",
"packets_out": "17",
"policyid": "1",
"policytype": "policy",
"poluuid": "ccb269e0-5735-51e9-a218-a397dd08b7eb",
"product": "Firewall",
"product_version": "50",
"proto": "6",
"protocol": "ip",
"protocol_version": "ipv4",
"rcvdbyte": "1224",
"rcvdpkt": "16",
"rule": "ccb269e0-5735-51e9-a218-a397dd08b7eb",
"rule_id": "1",
"sentbyte": "1188",
"sentpkt": "17",
"service": "HTTP",
"session_id": "105048",
"sessionid": "105048",
"source": "http:docs-fortigate",
"sourcetype": "fortigate_traffic",
"src": "10.1.100.11",
"src_interface": "port12",
"src_ip": "10.1.100.11",
"src_mac": "a2:e9:00:ec:40:01",
"src_port": "58012",
"src_translated_ip": "172.16.200.2",
"src_translated_port": "58012",
"src_zone": "undefined",
"srccountry": "Reserved",
"srcintf": "port12",
"srcintfrole": "undefined",
"srcip": "10.1.100.11",
"srcmac": "a2:e9:00:ec:40:01",
"srcport": "58012",
"srcserver": "0",
"srcuuid": "ae28f494-5735-51e9-f247-d1d2ce663f4b",
"subtype": "forward",
"time": "11:37:47",
"trandisp": "snat",
"transip": "172.16.200.2",
"transport": "tcp",
"type": "traffic",
"utmaction": "allow",
"utmref": "65500-742",
"vd": "vdom1",
"vendor": "Fortinet",
"vendor_action": "close",
"vendor_product": "Fortinet Firewall",
"vendor_transport": "58012"
}
FortiGate UTM logs
Pipeline condition: sourcetype="fgt_utm" OR sourcetype="fortigate_utm"
FortiGate UTM logs records security information from Unified Threat Management (UTM) events. See the FortiGate documentation for example events.
Example of extracted user attributes
{
"action": "blocked",
"agent": "curl/7.47.0",
"analyticscksum": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f",
"analyticssubmit": "false",
"app": "HTTP",
"category": "EICAR_TEST_FILE",
"craction": "2",
"crlevel": "critical",
"crscore": "50",
"date": "2026-02-18",
"dest": "172.16.200.55",
"dest_interface": "port11",
"dest_ip": "172.16.200.55",
"dest_port": "80",
"dest_zone": "undefined",
"direction": "incoming",
"dstintf": "port11",
"dstintfrole": "undefined",
"dstip": "172.16.200.55",
"dstport": "80",
"dtype": "Virus",
"eventtime": "1557773103767393505",
"eventtype": "infected",
"file_hash": "275a021bbfb6489e54d471899f7db9d1663fc695ec2fe2a2c4538aabf651fd0f",
"file_name": "eicar.com",
"file_path": "http://172.16.200.55/virus/eicar.com",
"filename": "eicar.com",
"ftnt_action": "blocked",
"http_user_agent": "curl/7.47.0",
"ids_type": "network",
"index": "docs-fortigate",
"level": "warning",
"logid": "0211008192",
"msg": "File is infected.",
"policyid": "4",
"product": "Firewall",
"product_version": "50",
"profile": "g-default",
"proto": "6",
"protocol": "ip",
"protocol_version": "ipv4",
"quarskip": "File-was-not-quarantined.",
"ref": "http://www.fortinet.com/ve?vn=EICAR_TEST_FILE",
"rule_id": "4",
"service": "HTTP",
"session_id": "359260",
"sessionid": "359260",
"severity": "critical",
"signature": "EICAR_TEST_FILE",
"source": "http:docs-fortigate",
"sourcetype": "fortigate_utm",
"src": "10.1.100.11",
"src_interface": "port12",
"src_ip": "10.1.100.11",
"src_port": "60446",
"src_zone": "undefined",
"srcintf": "port12",
"srcintfrole": "undefined",
"srcip": "10.1.100.11",
"srcport": "60446",
"subtype": "virus",
"time": "11:45:03",
"transport": "tcp",
"type": "utm",
"url": "http://172.16.200.55/virus/eicar.com",
"vd": "vdom1",
"vendor": "Fortinet",
"vendor_action": "blocked",
"vendor_eventtype": "infected",
"vendor_product": "Fortinet Firewall",
"vendor_url": "http://172.16.200.55/virus/eicar.com",
"virus": "EICAR_TEST_FILE",
"virusid": "2172"
}
VPC flow logs
Pipeline condition: sourcetype=aws:cloudwatchlogs:vpcflow
Amazon VPC flow logs are a feature of AWS Virtual Private Cloud (VPC) that capture metadata about the IP traffic going to and from network interfaces in your VPC. Extracted user attributes in Lumi include source and destination IP addresses, ports, protocol, and action. See the AWS documentation for example events.
Example of extracted user attributes
{
"message": "2 422682147474 eni-0635052fdd001dbfa 10.210.72.205 10.90.0.105 57752 9997 17 20 3303 1756736406 1756736427 REJECT OK",
"account_id": "422682147474",
"action": "blocked",
"app": "AWS VPC Flow Logs",
"aws_account_id": "422682147474",
"bytes": 3303,
"dst": "10.90.0.105",
"dst_ip": "10.90.0.105",
"dst_port": 9997,
"duration": 21,
"dvc": "eni-0635052fdd001dbfa",
"end_time": 1756736427,
"eventtype": "vpcflow ( cloud communicate network )",
"host": "web-01",
"index": "main",
"interface_id": "eni-0635052fdd001dbfa",
"log_status": "OK",
"packets": 20,
"protocol": "ip",
"protocol_code": 17,
"protocol_full_name": "User Datagram",
"protocol_version": "IPV4",
"source": "vpc-example.log",
"sourcetype": "aws:cloudwatchlogs:vpcflow",
"src": "10.210.72.205",
"src_ip": "10.210.72.205",
"src_port": 57752,
"start_time": 1756736406,
"transport": "udp",
"user_id": "422682147474",
"vendor_account": "422682147474",
"vendor_product": "AWS VPC Flow Logs",
"version": 2,
"vpcflow_action": "REJECT",
"eventId": "e_h5cc5116a-1757079660000-11-952-709-2",
"receiver": "splunk.s3",
"team": "Unassigned",
"env": "Unknown",
"iamKeyId": "75700224-47b0-498a-b76e-4f0aab3a73e7",
"processor": "ec 20250905.1661.0",
"collector": "ec 20250905.1661.0"
}
Windows event logs
Pipeline condition: Windows-specific sourcetype and source values
Windows predefined pipeline conditions
sourcetype = "ActiveDirectory" OR
sourcetype = "DhcpSrvLog" OR
sourcetype = "WinEventLog" OR
sourcetype = "WinEventLog:*" OR
sourcetype = "XmlWinEventLog" OR
sourcetype = "XmlWinEventLog:*" OR
sourcetype = "WindowsUpdateLog" OR
sourcetype = "WinRegistry" OR
sourcetype = "WinHostMon" OR
sourcetype = "wmi" OR
sourcetype = "WMI:*" OR
sourcetype = "Perfmon:*" OR
sourcetype = "PerfmonMk:*" OR
sourcetype = "MSAD:*" OR
sourcetype = "Script:*" OR
source = "*WindowsUpdate.Log" OR
source = "WMI*" OR
source = "WinEventLog*" OR
source = "XmlWinEventLog*" OR
host = "WinEventLogForwardHost"
Windows event logs capture events for the Microsoft Windows operating system and applications that run on it. Extracted user attributes in Lumi include computer name, error code, and event code.
The predefined pipeline operates on a general set of Windows event logs which can have different attributes depending on their origin and purpose. This is the same set of logs processed by the Splunk® Add-on for Microsoft Windows. For example:
- Core logs (
sourcetype=WinEventLog) - XML-formatted logs (
sourcetype=XmlWinEventLog) - Performance metrics (
sourcetype=Perfmon:*)
For an end-to-end example of using Windows event logs with Lumi, see How to send Windows event logs with S3 routing.
Example of extracted user attributes
{
"message": "10/01/2025 04:47:46 PM LogName=System EventCode=7036 EventType=4 ComputerName=EC2AMAZ-EXAMPLE SourceName=Microsoft-Windows-Service Control Manager Type=Information RecordNumber=145454 Keywords=Classic TaskCategory=None OpCode=The operation completed successfully. Message=The Microsoft Account Sign-in Assistant service entered the stopped state.",
"ComputerName": "EC2AMAZ-EXAMPLE",
"Error_Code": null,
"EventCode": 7036,
"EventType": 4,
"Keywords": "Classic",
"LogName": "System",
"Message": "The Microsoft Account Sign-in Assistant service entered the stopped state.",
"OpCode": "The operation completed successfully.",
"RecordNumber": 145454,
"Service_Name": "Microsoft Account Sign-in Assistant",
"SourceName": "Microsoft-Windows-Service Control Manager",
"TaskCategory": "None",
"Type": "Information",
"_cooked": "_cooked",
"_path": "C:\\Program Files\\MyApplication\\bin\\myapp.exe",
"_pre_msg": "10/01/2025 04:47:46 PM LogName=System EventCode=7036 EventType=4 ComputerName=EC2AMAZ-EXAMPLE SourceName=Microsoft-Windows-Service Control Manager Type=Information RecordNumber=145454 Keywords=Classic TaskCategory=None OpCode=The operation completed successfully.",
"_savedHost": "host::10.103.103.144",
"_savedPort": 9998,
"_sourcetype": "WinEventLog:System",
"body": "The Microsoft Account Sign-in Assistant service entered the stopped state.",
"category": "None",
"dest": "EC2AMAZ-EXAMPLE",
"dvc": "EC2AMAZ-EXAMPLE",
"dvc_nt_host": "EC2AMAZ-EXAMPLE",
"event_id": 145454,
"hf_proxy": "meta_test",
"host": "EC2AMAZ-EXAMPLE",
"id": 145454,
"index": "wineventlog",
"package": 7036,
"product": "Windows",
"remoteport": 51391,
"service": "Microsoft Account Sign-in Assistant",
"service_name": "Microsoft Account Sign-in Assistant",
"severity_id": 4,
"signature_id": 7036,
"source": "WinEventLog:System",
"sourcetype": "WinEventLog",
"status": "stopped",
"vendor": "Microsoft",
"vendor_product": "Microsoft Windows"
}
Learn more
See the following topics for more information:
- Work with predefined pipelines to learn about predefined pipelines and how to use them.
- Transform events using pipelines for an overview of pipelines and processors.
- Manage pipelines and processors for how to create and manage pipelines and processors.